Near Field Communication (NFC) Overview
Near Field Communication (NFC) technology has become an integral part of our daily lives, enabling seamless communication and data exchange between electronic devices in very close proximity. NFC operates within a short-range wireless communication standard, allowing devices to establish a connection without the need for complex setups or pairing processes. This technology has applications across various industries due to its versatility, security features, and ease of use.
The NFC Forum is the organization responsible for developing the NFC specification, ensuring interoperability amongst devices and services, and educating the market about its technology. Global support is achieved by using the 13.56 MHz unlicensed ISM band based on the ISO/IEC 18000-3 air interface standard.
NFC devices can be used to quickly transfer information for applications with a sample of use cases below:
- Payment terminal and credit card payments – NFC-enabled smartphones can be used as digital wallets, allowing users to make contactless payments at retail stores, restaurants, and public transportation terminals.
- Room key and hotel door lock – Secure access control in buildings, events, and vehicles. This includes keyless entry systems, electronic ticketing, and secure authentication.
- Data exchange – For instance, tapping two NFC-enabled smartphones can quickly share contact information, URLs, or files. Examples include contact sharing (i.e. Dot) or having NFCs embedded in posters or advertisements, enabling users to access additional information, promotional offers, or download content by simply tapping their devices. Finally, the Adidas Telstar 18 football allows users to connect and interact with the ball.
- Bootstrapping – Setting up the connection between devices to use a more capable wireless technology such as Bluetooth or Wi-Fi. NFC can be used on IoT devices or Wi-Fi access points for initial connection and onboarding.
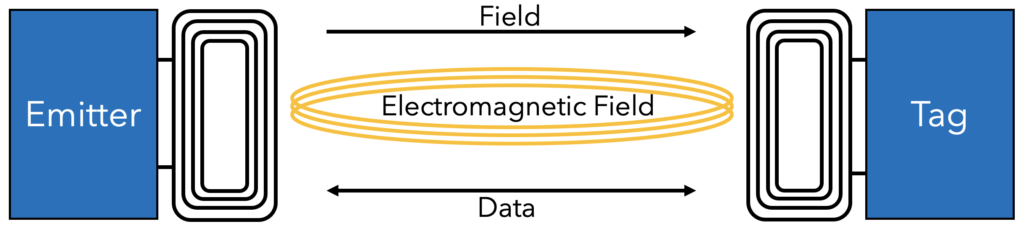
RF Circuit
As mentioned, NFC technology operates in the 13.56 MHz frequency range, using inductive coupling to enable communication between devices. This is the reason many NFCs circuits do not require an internal power supply – the induced field generates enough current to power a circuit and transmit the necessary data.
The RF circuit consists of two coils: one in the initiator device and the other in the target device. When these coils come into very close proximity, they create a magnetic field that allows data transfer between the devices. Proximity is in the typical intended operating range of 0-10 cm (0-3.94 in) between the transmitter and receiver, but higher transmit power or antennas with higher gain can extend this distance. The NFC Forum describes the NFC range of communication as >2 cm (or one inch).
Modes of communication
NFC supports two main modes of communication, along with a hybrid mode:
Active Communication Mode: In this mode, both devices generate their own RF fields, allowing for faster data exchange but consuming more power.
Passive Communication Mode: Here, one device generates an RF field, and the other device uses this field for communication. This mode is more energy-efficient but generally slower.
Semi-Passive Tags: In this mode, both devices are powered by a battery but only become active when in the presence of an NFC reader. They combine some benefits of both passive and active tags.
Modes of Operation
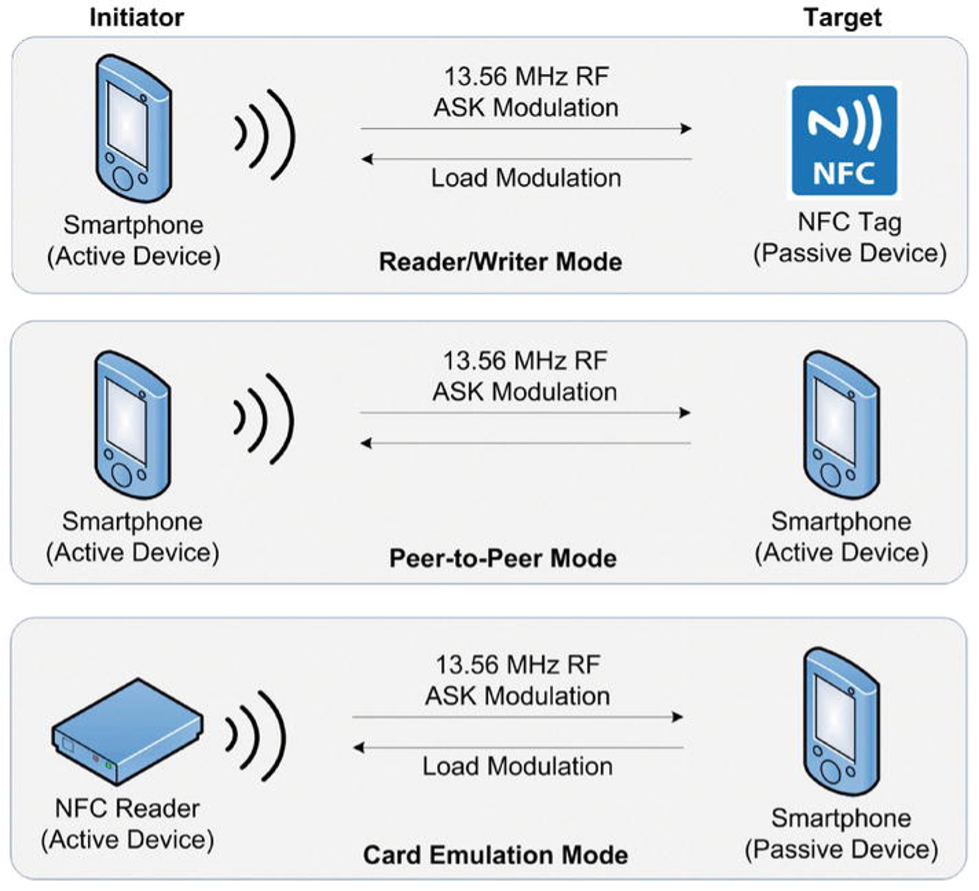
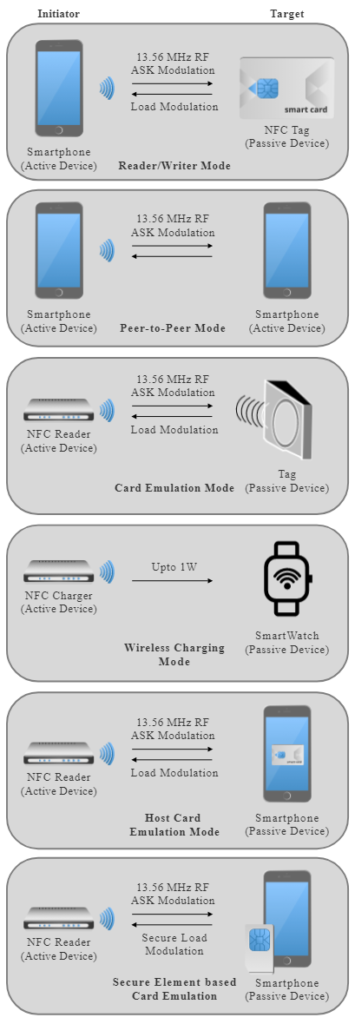
NFC supports three main modes of operation, along with two emulation modes and a wireless charging mode:
Reader/Writer Mode: In this mode, an active NFC device (reader) communicates with passive NFC tags or other active devices (writers) to read or write data.
Peer-to-Peer Mode: Two active NFC devices can communicate with each other to exchange data. This mode is often used for tasks like file sharing, contact exchange, and multiplayer gaming.
Card Emulation Mode: An NFC device can emulate a contactless smart card, allowing it to interact with existing infrastructure like contactless payment terminals. This enables mobile payment and access control applications. In this configuration, an HCE app running on the Device Host emulates the contactless card. The NFC controller forwards all received contactless commands to the Device Host, allowing the HCE app to communicate with the contactless reader device via the NFC API.
Wireless Charging Mode: Up to 1W of power can be transferred to the NFC connection. Small devices with limited power supplies, such as a stylus, headset, fitness tracker, or other small products, can charge using this mode.
Host Card Emulation: In this configuration, an HCE app running on the Device Host emulates the contactless card. The NFC controller forwards all received contactless commands to the Device Host, allowing the HCE app to communicate with the contactless reader device via the NFC API.
Secure Element based Card Emulation: A secure element inside the NFC device emulates the contactless card. The secure element can be either a security chip embedded in the NFC device or an installed NFC-enabled SIM card. In either case, the commands received from the contactless reader will be forwarded to the secure element for processing, allowing the same high-security level for transactions as those processed by contactless smart card solutions.
Tag Types
The four types of tags referred to by ISO-14443-A are as follows:
| Tag Type | Communcation Speed | Memory | Anti-Collision | Preconfigured to be RO or R/W | Reference Standard |
|---|---|---|---|---|---|
| 1 | throughput 106kbps | 768 bits (96 bytes) – 16kb (2kB) | No | No | ISO-14443A |
| 2 | throughput 106kbps | 768 bits (96 bytes) – 16kb (2kB) | Yes | No | ISO-14443A |
| 3 | 212 or 424kbps | up to 8Mb (1MB) | Yes | Yes | Japanese Industrial Standard (JIS) X 6319-4 |
| 4 | 106 or 212 or 424kbps | up to 256kb (32kB) | Yes | Yes | ISO-14443A and ISO-14443B |
As defined in ISO/IEC 18000-3, NFC uses two different coding types to transfer data. When an active device transfers data at 106 kbps, a modified Miller coding with 100% modulation is used. For all other rates, Manchester coding is used with a modulation ratio of 10%.
| Speed (kbps) | Active Device | Passive Device |
|---|---|---|
| 424 | Manchester, 10% ASK | Manchester, 10% ASK |
| 212 | Manchester, 10% ASK | Manchester, 10% ASK |
| 106 | Modified Miller, 100% ASK | Manchester, 10% ASK |
During the anti-collision phase, three or four different frames are received from a tag (ATQA, UID, SAK and optional ATS).
The ATQA, SAK and ATS values can be used to identify the manufacturer, tag type and application. However, it’s not recommended to rely on ATQA due to potential collision when more than one target is in the field.
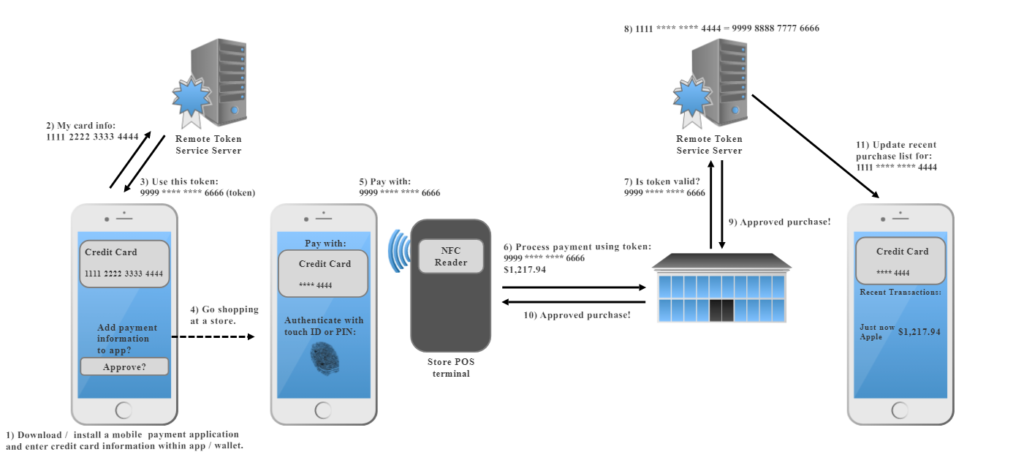
Data Flow
The following graphic represents the data flow used to create a token and then authorize a purchase at a store using an NFC to facilitate payment via credit card information stored in a mobile app or wallet.
Slàinte!
Resources
NFC Forum
RFID & NFC (Mouser Electronics)
https://www.mouser.ca/applications/rfid-nfc-introduction/
ISO/IEC 18000-3:2010
Information Technology – Radio frequency identification for item management – Part 3: Parameters for air interface communications at 13.56 MHz
https://www.iso.org/standard/53424.html
ISO/IEC 14443-1:2018
Cards and security devices for personal identification – Contactless proximity objects – Part 1: Physical characteristics
https://www.iso.org/standard/73596.html
ISO/IEC 14443-2:2020
Cards and security devices for personal identification – Contactless proximity objects – Part 2: Radio frequency power and signal interference
https://www.iso.org/standard/73597.html
ISO/IEC 14443-3:2018
Cards and security devices for personal identification – Contactless proximity objects – Part 3: Initialization and anticollision
https://www.iso.org/standard/73598.html
ISO/IEC 14443-4:2018
Cards and security devices for personal identification – Contactless proximity objects – Part 4: Transmission protocol